
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
This document describes the process to generate certificates that have to be uploaded with every fresh installation of Secure Console Private Cloud or to renew the installed Certificate Services.
The information in this document is based on these software and hardware versions:
Cisco recommends that you have knowledge of these topics:
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
With the introduction of Secure Console Private Cloud 3.X, hostnames, and certificate/key pairs are required for all of the following services:
This document is discussed a quick way to generate and upload the required certificates. You can tweak each of the parameters, including the hashing algorithm, key size, and others, as per your organization's policy, and your mechanism of generating these certificates might not match with what is detailed here.
Warning: The procedure mentioned below can vary as per your CA server configuration. It is expected that the CA server of your choice is already provisioned and the configuration of the same has been completed. The following technote just describes an example of generating the certificates and Cisco TAC is not involved in troubleshooting issues related to certificate generation and/or CA server issues of any kind.
Ensure that the following roles are installed and configured on your Windows Server.

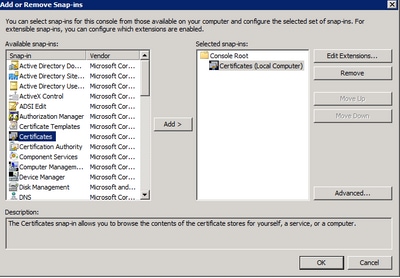
Step 1. Navigate to MMC console, and add the Certificates snap-in for your computer account as shown in the image here.
Step 2. Drill down Certificates (Local Computer) > Personal > Certificates.
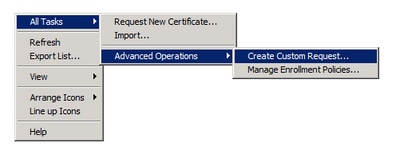
Step 3. Right-click on the empty space and select All Tasks > Advanced Operations > Create Custom Request.
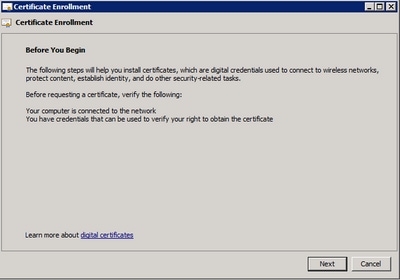
Step 4. Select Next at the Enrollment window.
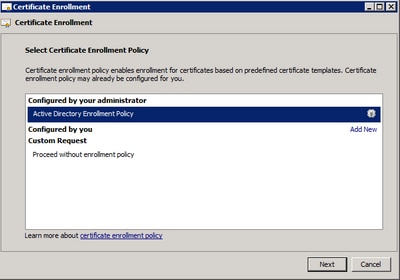
Step 5. Select your certificate enrollment policy and select Next.
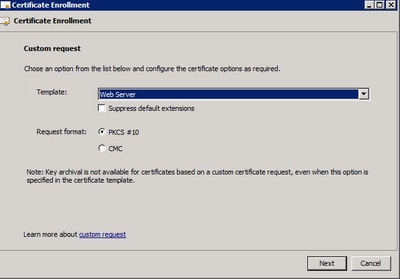
Step 6. Choose the template as Web Server and select Next.
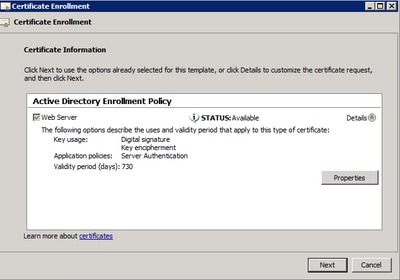
Step 7. If your "Web Server" template has been configured correctly and is available for enrollment, the status Available is displayed. Select Details to expand Properties.
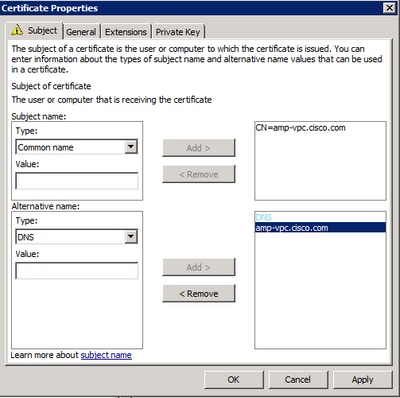
Step 8. At a minimum, add the CN and DNS attributes. The rest of the attributes can be added as per your security requirements.
Step 9. Optionally, give a Friendly Name under the General tab.
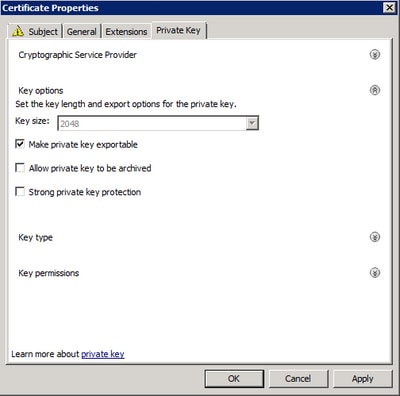
Step 10. Select on the Private Key tab and ensure that you're enabling Make private key exportable under the Key Options section.
Step 11. Finally, select on OK. This must lead you to the Certificate Enrollment dialog from where you can select Next.
Step 12. Browse to a location to save the .req file which is submitted to the CA server for signing.
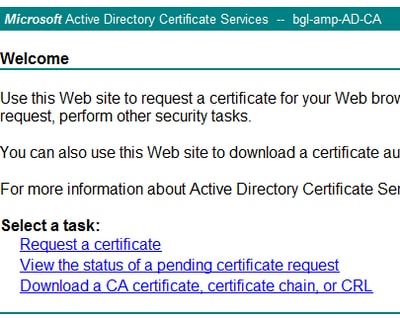
Step 1. Navigate to your MS AD Certificate Services Web Page as below and select Request a Certificate.
Step 2. Select on the advanced certificate request link.
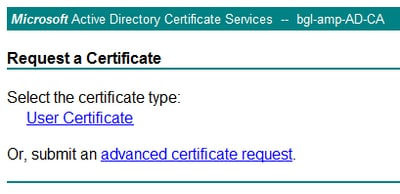
Step 3. Select on Submit a certificate request by using a base-64-encoded CMC or PKCS #10 file, or submit a renewal request by using a base-64-encoded PKCS #7 file.
Step 4. Open the contents of the previously saved .req file (CSR) via Notepad. Copy the contents and paste it here. Ensure that the Certificate Template is selected as Web Server
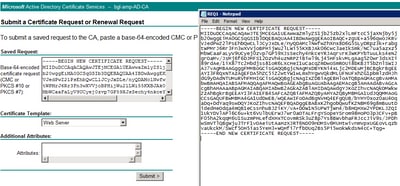
Step 5. Finally, select Submit.
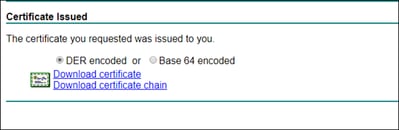
Step 6. At this point, you must be able to Download the certificate, as shown in the image.
Step 1. Install the certificate into your Certificate Store by opening the .cer file and select Install Certificate.
Step 2. Navigate to the MMC snap-in that was selected earlier.
Step 3. Navigate to the store where the certificate was installed.
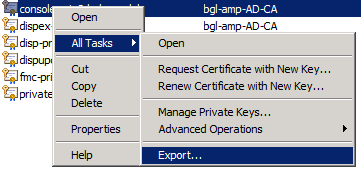
Step 4. Right-click the correct certificate, select All Tasks > Export.
Step 5. At the Certificate Export Wizard, confirm to export the private key, as shown in the image.
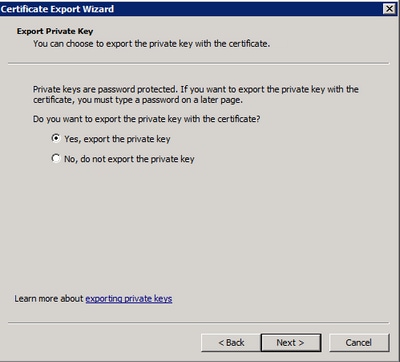
Step 6. Enter a password and select Next to save the private key on your disk.
Step 7. This saves the private key in .PFX format, however, this needs to be converted to .PEM format to use this with Secure Endpoint Private Cloud.
Step 8. Install OpenSSL libraries.
Step 9. Open a command prompt window and change to the directory where you installed OpenSSL.
Step 10. Run the following command to extract the private key and save it to a new file: (If your PFX file is not in the same path as where the OpenSSL library is stored, you have to specify the exact path along with the filename)
openssl pkcs12 -in yourpfxfile.pfx -nocerts -out privatekey.pem -nodes
Step 11. Now run the following command to also extract the public cert and save it to a new file:
openssl pkcs12 -in yourpfxfile.pfx -nokeys -out publiccert.pem -nodes
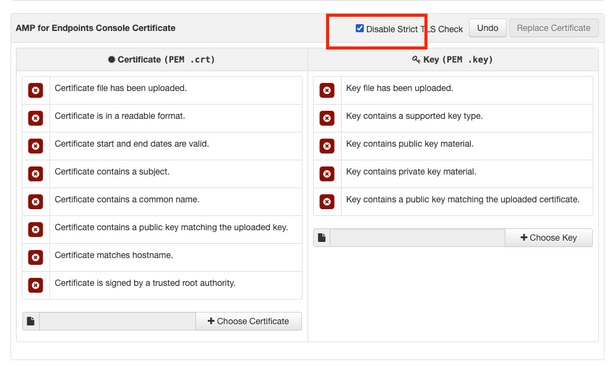
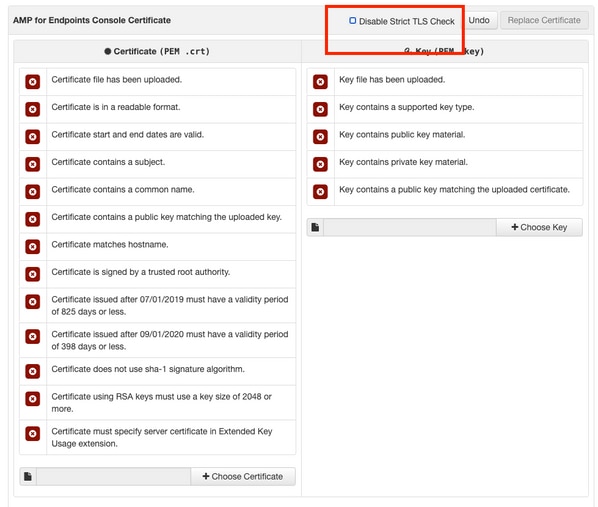
Note: Strict TLS Check verifies that the certificate meets Apple’s TLS requirements. Please refer to the Admin Guide for more information.
Ensure that the Linux Server that you're trying to generate the required certificates has the OpenSSL 1.1.1 libraries installed. Verifying if this and the procedure listed below can vary from the Linux distribution that you're running. This portion has been documented, as done on a CentOS 8.4 Server.
Step 1. Generate the Private Key for Root CA certificate.
openssl genrsa -out 4096
Step 2. Generate the CA certificate.
openssl req \
-subj '/CN=/C=US/OU=/O=' \
-addext "extendedKeyUsage = serverAuth, clientAuth" \
-outform pem -out \
-key -new -x509 \
-days "1000"
Create the certificate for Authentication, Console, Disposition, Disposition-Extended, Update server, Firepower Management Center(FMC) service as per the DNS name entry. You need to repeat the below certificate generate process for each service (Authentication, Console etc.).
openssl genrsa -out 4096
Replace the with the new KEY filename to be created as Auth-Cert.key
openssl req -new \
-subj '/CN=/C=US/OU=/O=' \
-key -out
Replace the with the current (or new) certificate KEY file such as Auth-Cert.key
Replace the with CSR filename to be created such as Auth-Cert.crt
openssl x509 -req \
-in -CA \
-CAkey -CAcreateserial -out \
-days 397 -sha256
Replace the with actual (or new) certificate CSR such as Auth-Cert.csr
Replace the with actual (or new) PEM filename as RootCAName.pem
Replace the with the current (or new) certificate KEY file such as Auth-Cert.key
Replace the with filename to be created such as Auth-Cert.crt
Note: Strict TLS Check verifies that the certificate meets Apple’s TLS requirements. Please refer to the Admin Guide for more information.
Step 1. Generate the Private Key for Root CA certificate.
openssl genrsa -out 4096
Step 2. Generate the CA certificate.
openssl req \
-subj '/CN=/C=US/OU=/O=' \
-outform pem -out \
-key -new -x509 \
-days "1000"
Create the certificate for Authentication, Console, Disposition, Disposition-Extended, Update server, Firepower Management Center(FMC) service as per the DNS name entry. You need to repeat the below certificate generate process for each service (Authentication, Console etc.).
[v3_ca]
basicConstraints = CA:FALSE
keyUsage = critical, digitalSignature, keyEncipherment
extendedKeyUsage = critical, serverAuth, clientAuth
openssl genrsa -out 4096
Replace the with a new KEY filename to be created as Auth-Cert.key
openssl req -new \
-key \
-subj '/CN=/C=US/OU=/O=' \
-out
Replace the with the current (or new) certificate KEY such as Auth-Cert.key
Replace the with the current (or new) certificate CSR such as Auth-Cert.csr
openssl x509 -req -in \
-CA -CAkey \
-CAcreateserial -out \
-extensions v3_ca -extfile extensions.cnf \
-days 397 -sha256
Replace the with current (or new) certificate CSR such as Auth-Cert.csr
Replace the with current (or new) PEM filename as RootCAName.pem
Replace the with current (or new) certificate KEY file such as Auth-Cert.key
Replace the with filename to be created such as Auth-Cert.crt
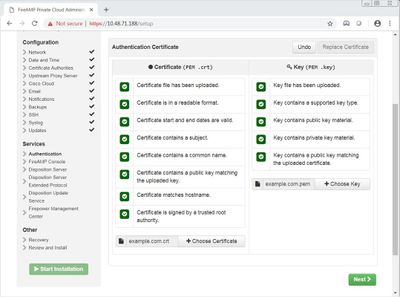
Step 1. Once the certificates are generated from any of the above methods, upload the corresponding certificate for each of the services. If they have been generated correctly, all the checkmarks are enabled as seen in the image here.
There is currently no verification procedure available for this configuration.
There is currently no specific troubleshooting information available for this configuration.